Overview
EscapeCloud Platform is a self-hosted cloud exit readiness platform for assessing public cloud infrastructure.
This documentation covers the public technical overview of the EscapeCloud Platform, with a focus on architecture, deployment, and high-level security boundaries.
Platform Scope
EscapeCloud Platform combines the components required to deliver the web application, assessment engine, and supporting infrastructure as a single operational platform.
This documentation provides a high-level view of:
- platform architecture
- core components
- deployment options
- security concepts at infrastructure level
Deployment Options
EscapeCloud Platform can be deployed in different ways depending on the target environment.
Kubernetes
Kubernetes-based deployment using Helm charts for structured, repeatable platform installation.
Docker Compose
Container-based deployment for simpler local, evaluation, or smaller-scale environments.
Documentation Scope
This site is limited to public platform documentation.
Operational product guidance and deeper implementation detail are provided separately within the product or during onboarding and evaluation.
Architecture
EscapeCloud Platform is deployed within customer-controlled infrastructure and is composed of a web-facing application layer, background processing, and supporting data services.
The platform can be deployed using Docker Compose or Helm, depending on the target environment and operational requirements.
High-Level Architecture
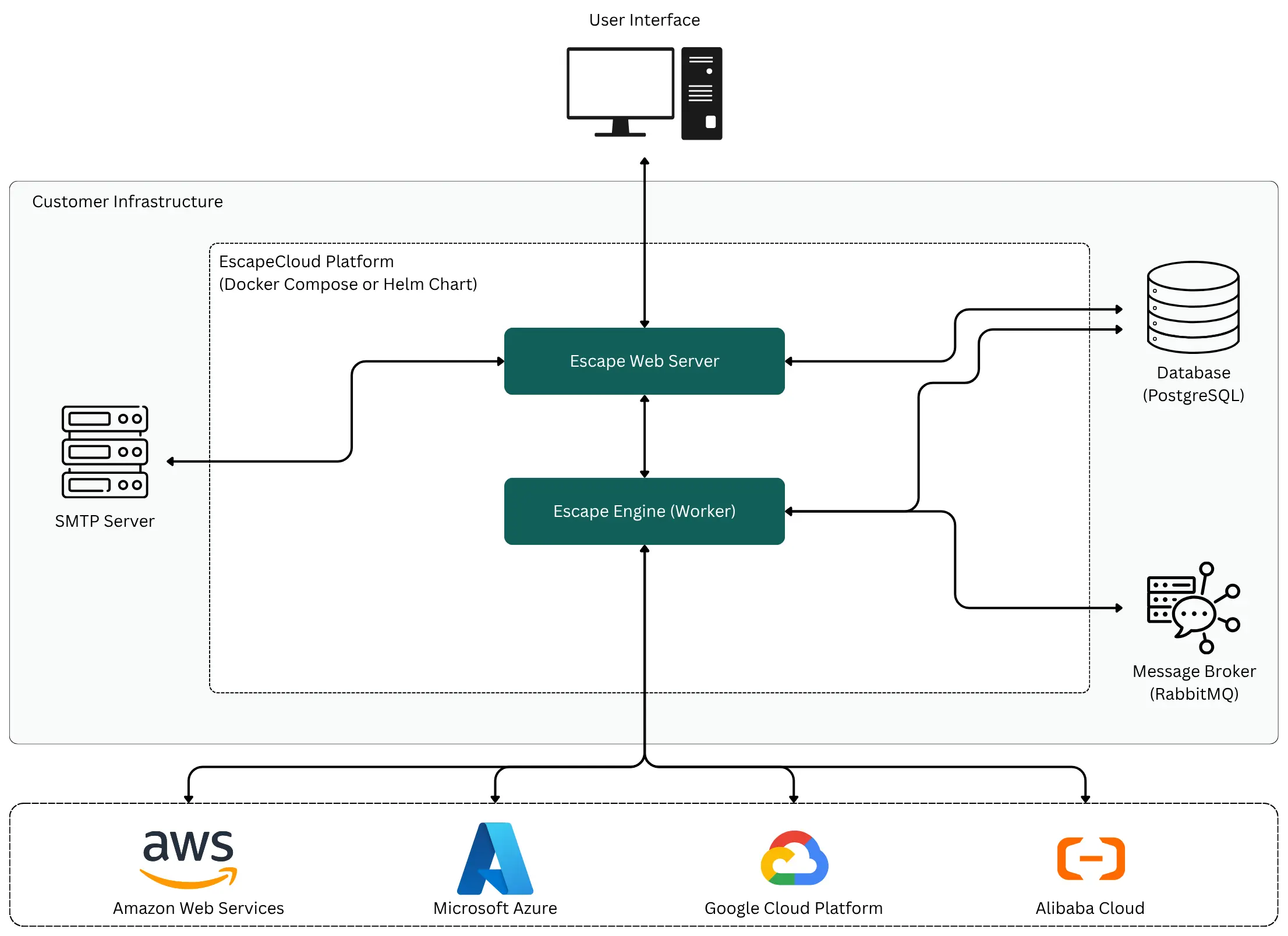
The diagram shows the high-level runtime boundary of the platform, including the user-facing application, background worker services, database, message broker, and cloud provider integrations.
Platform Interaction Model
- The Web Application provides the primary user interface for interacting with the platform.
- The Assessment Engine handles background processing and platform-side execution.
- PostgreSQL provides persistent platform storage.
- RabbitMQ provides messaging between platform services and background tasks.
- SMTP integration supports outbound notification delivery.
- The platform interacts with supported public cloud providers for assessment and analysis.
Architecture Scope
This section describes the high-level platform structure only. It does not cover internal assessment logic, product workflows, or implementation-specific processing behavior.
Components
EscapeCloud Platform consists of platform services deployed within customer-controlled infrastructure together with a small set of supporting infrastructure dependencies.
Platform Services
Web Application
The web application provides the primary user interface for interacting with EscapeCloud Platform.
Assessment Engine
The assessment engine provides the platform’s processing and service execution layer, including background processing and internal platform operations.
Infrastructure Dependencies
Database
The platform requires a relational database for persistent storage. PostgreSQL is currently the supported database backend.
Message Queue
The platform requires a messaging component for asynchronous communication and task coordination. RabbitMQ is currently the supported messaging backend.
SMTP
SMTP is used for outbound email delivery and notification-related messaging. This is typically provided by the customer environment, although managed SMTP support can be arranged for specific deployment requirements.
Deployment Models
EscapeCloud Platform supports multiple deployment approaches depending on the target environment and operational requirements.
Kubernetes (Helm)
Kubernetes deployment is intended for structured, production-oriented environments where platform workloads are managed within an existing cluster.
This approach is suitable when the target environment already provides core infrastructure services such as database, messaging, ingress, DNS, and certificate management.
Public repository: escapecloud_helm_charts
Docker Compose
Docker Compose provides a simpler deployment model for evaluation, local installation, or smaller-scale environments.
This approach can be used with external infrastructure services or with selected containerized dependencies included alongside the platform.
Public repository: escapecloud_docker_compose
Deployment Considerations
The appropriate deployment model depends on:
- target environment maturity
- infrastructure ownership model
- operational requirements
- external dependency strategy
- networking and certificate handling approach
Kubernetes (Helm)
EscapeCloud Platform can be deployed to Kubernetes using the provided Helm chart.
This deployment approach is intended for structured, production-oriented environments where platform workloads run inside an existing Kubernetes cluster and supporting infrastructure is managed separately.
Deployment Scope
The Helm chart deploys the EscapeCloud Platform workloads and internal Kubernetes services required for application operation.
This includes:
- platform application workloads
- internal Kubernetes Service resources
- one-time bootstrap jobs
- scheduled CronJobs
External Infrastructure
The Helm chart expects supporting infrastructure to be available outside of the chart itself.
This includes:
- database (PostgreSQL)
- message queue (RabbitMQ)
- container registry access
- DNS
- Gateway or Ingress
- TLS certificates and renewal
Prerequisites
Before deployment, the target environment should provide:
- Kubernetes cluster access
- Helm
- a target namespace
- access to the EscapeCloud container registry
- a supported database backend
- a supported message queue backend
Configuration
Deployment is configured through a values.yaml file.
Typical configuration areas include:
- hostname
- image tags
- image pull credentials
- database connection settings
- message queue connection settings
- application secrets
Installation Flow
- Prepare the target namespace and external infrastructure dependencies.
- Copy the sample values file and create an environment-specific
values.yaml. - Configure image tags, hostname, secrets, and infrastructure connection details.
- Install or upgrade the chart with Helm.
- Verify workload readiness, bootstrap jobs, and service availability.
Networking
The Helm chart creates internal Kubernetes Services only.
External access is expected to be handled separately through the target Gateway or Ingress layer.
Public Repository
Docker Compose
EscapeCloud Platform can be deployed with Docker Compose for evaluation, local installation, and simpler runtime environments.
This deployment approach provides a more compact setup model and can be used either with external infrastructure services or with selected containerized dependencies alongside the platform.
Deployment Scope
The Docker Compose stack runs the main EscapeCloud Platform services required for application operation.
Depending on the deployment approach, supporting services may be provided either externally or through containerized dependencies included with the stack.
Infrastructure Dependencies
The platform requires supporting infrastructure for persistent storage, messaging, and outbound email delivery.
Depending on the target environment, these may be:
- provided externally by the customer environment
- deployed alongside the platform where supported
Prerequisites
Before deployment, the target host should provide:
- Docker Engine
- Docker Compose
- access to the EscapeCloud container registry
- reachable network ports for platform access
- DNS pointing to the host when public access is required
For HTTPS deployments, certificate material is also required.
Configuration
Deployment is configured through a .env file derived from the provided environment template.
Typical configuration areas include:
- hostname
- image tags
- database connection settings
- message queue connection settings
- TLS certificate settings
Installation Flow
- Copy the provided environment template to a local
.envfile. - Configure platform, infrastructure, and certificate values as required.
- Pull images if needed.
- Start the platform with Docker Compose.
- Validate application reachability and service startup.
HTTP and HTTPS
Docker Compose deployments can be configured for either HTTP-only access or HTTPS access, depending on the provided certificate settings.
Where HTTPS is required, certificate files and related configuration must be available on the deployment host.
Public Repository
Security Overview
EscapeCloud Platform is designed to run within customer-controlled infrastructure.
For self-hosted deployments, the platform operates inside environment boundaries defined by the customer, with supporting infrastructure and external access managed according to the target deployment architecture.
Deployment Boundary
EscapeCloud Platform is deployed within customer-managed infrastructure using either Kubernetes or Docker Compose, depending on the selected deployment approach.
This model allows the customer to define network boundaries, runtime isolation, access controls, and supporting infrastructure according to internal security and operational requirements.
Infrastructure Separation
The platform services operate together with a small set of supporting infrastructure dependencies, including database, messaging, and outbound email delivery.
These dependencies can be integrated into the customer environment in a way that aligns with existing infrastructure, operational controls, and security policies.
Operational Control
In self-hosted deployments, the customer retains control over:
- infrastructure boundaries
- network exposure
- access management
- certificate handling
- supporting infrastructure services
Public Documentation Scope
This page provides a high-level overview of the platform security boundary only.
Detailed hardening guidance, implementation-specific controls, and deployment-specific security configuration are handled separately during onboarding and evaluation.
Repositories
This page links to the public repositories related to EscapeCloud Platform deployment and evaluation.
Helm Charts
Helm charts for deploying EscapeCloud Platform to Kubernetes environments.
Repository: escapecloud_helm_charts
Docker Compose
Docker Compose deployment assets for local installation, evaluation, and simpler runtime environments.
Repository: escapecloud_docker_compose
Core Platform / Open Source
Public source repository for the open-source EscapeCloud components.
Repository: cloudexit
Notes
These public repositories provide deployment assets and related platform materials intended for public use.
Access & Support
Public documentation is intended to support technical evaluation of EscapeCloud Platform.
Documentation Scope
This site covers public architecture, deployment approaches, infrastructure dependencies, and the high-level security model of the platform.
Detailed implementation guidance, deployment-specific documentation, and onboarding materials are provided separately as part of evaluation and customer enablement.
Support
Support for deployment planning, onboarding, and platform evaluation is handled through the EscapeCloud team.
Contact
Email: info@escapecloud.hu
Book a demo: escapecloud.io/book-demo